Vassilis Kontoglis

AAFCPAs to Speak at 2026 Plan Sponsor Fiduciary Summit
AAFCPAs’ Shawn Huxley, CPA, MSA, Partner, Employee Benefit Plans and Vassilis Kontoglis, Partner, AI Digital Transformation & Security have been invited to speak at the 2026 Plan Sponsor Fiduciary Summit. Attendees will gain valuable insight from experienced professionals on navigating fiduciary challenges, including lessons from litigation, updates from Secure 2.0, strategies to prepare for plan […]
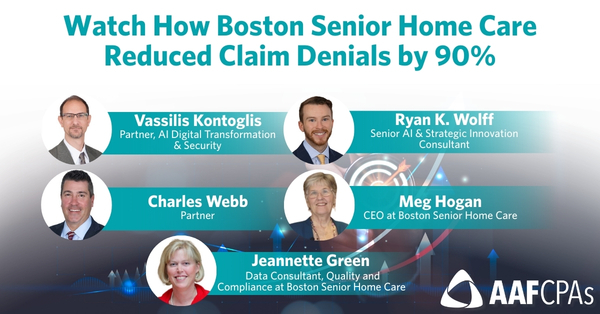
Watch How Boston Senior Home Care Reduced Claim Denials by 90% — A Live Client Webinar
Boston Senior Home Care slashed monthly claim denials from $65,000 to just $6,000 by automating one of the most time‑consuming, risk‑prone processes in their organization. Watch how this transformation delivered real‑time visibility, restored staff capacity, and created a proactive model any Aging Services Access Points (ASAPs) can replicate. Speakers include Vassilis Kontoglis, Partner, AI Digital […]

How IT Controls Keep Your Systems and Data Safe
During AAFCPAs’ recent webinar, Understanding Your ITGCs: Why They Matter and How to Strengthen Them (November 2025), Lisa Whittemore, CFE, CRMA, MBA and Vassilis Kontoglis presented a practical framework for assessing, strengthening, and monitoring IT general controls to protect data, ensure operational continuity, and support regulatory compliance. A single misstep in IT General Controls (ITGCs) […]

Start Small to Scale Smart with Automation
The idea of automation often arrives with fanfare—promises of transformation, efficiency, and sweeping change. But for many organizations, especially those already stretched thin, the prospect of overhauling core business processes may feel impractical. Automation does not have to begin with large-scale disruption. A focused, manageable start often leads to more effective outcomes. Starting with one […]

Building an Innovation Mindset for Automation Success
Organizations often approach automation as a technology upgrade—an efficiency project, a cost-saver, a way to modernize operations. But even the best-designed systems can falter without a culture that is ready to change. Resistance does not always sound like “no.” It may take the form of quiet hesitation, skepticism, or the reversion to old habits once […]

How Organizations Use AI to Monitor Systems and Respond to Threats
Artificial intelligence is reshaping how organizations think about system security and operational oversight. Unlike traditional tools built on fixed rules and reactive triggers, AI systems bring a capacity for adaptation—learning from patterns, anticipating irregularities, and flagging potential issues before they become disruptive. This shift not only makes systems more responsive but also gives IT and […]

Watch Understanding Your ITGCs: Why They Matter and How to Strengthen Them
IT General Controls (ITGCs) are under increasing scrutiny—and the consequences of failure are growing. CEOs, CFOs, and Boards are often blindsided by assessment findings, risk exceptions, and regulatory pressure tied to weak or outdated IT controls. These issues aren’t just technical—they’re strategic, with real implications for financial integrity, compliance, and reputation. In this webinar, we […]

There Are Automation Opportunities in Your Everyday Operations
Most organizations are busy enough just keeping up with daily responsibilities. When operations rely on habit and deadlines, it is easy to overlook the quiet drag of manual tasks, i.e. the form re-entered in three systems, the spreadsheet passed around for approvals, the weekly report that takes hours to compile. These inefficiencies often remain hidden […]

Take Action to Protect Your Organization During Cybersecurity Awareness Month
October marks Cybersecurity Awareness Month, a time to reflect on the safeguards that protect our organizations, communities, and critical systems. While cyber threats exist year-round, this month serves as a reminder to take concrete steps to reduce vulnerabilities and strengthen resilience. Every business, nonprofit, and mission-driven organization relies on systems and processes that must operate […]
